Banking Malware Exploiting Social Engineering Infects 248,000 Mobile Users
Mobile banking malware has surged dramatically in 2024, with nearly 248,000 users affected—an alarming 3.6 times increase from the 69,000 recorded in 2023.
This sharp rise, particularly in the latter half of the year, highlights a growing cybersecurity threat as cybercriminals increasingly exploit mobile platforms for financial fraud.
The Mamont malware family has emerged as the most prevalent threat, responsible for 36.7% of all mobile banking malware attacks. First detected in late 2023, Mamont primarily targets users in Russia and Commonwealth of Independent States (CIS) countries through sophisticated social engineering tactics.
Other significant threats include the Agent.rj variant (11.14%) and UdangaSteal.b (3.17%), both rapidly gaining traction in the mobile threat landscape.
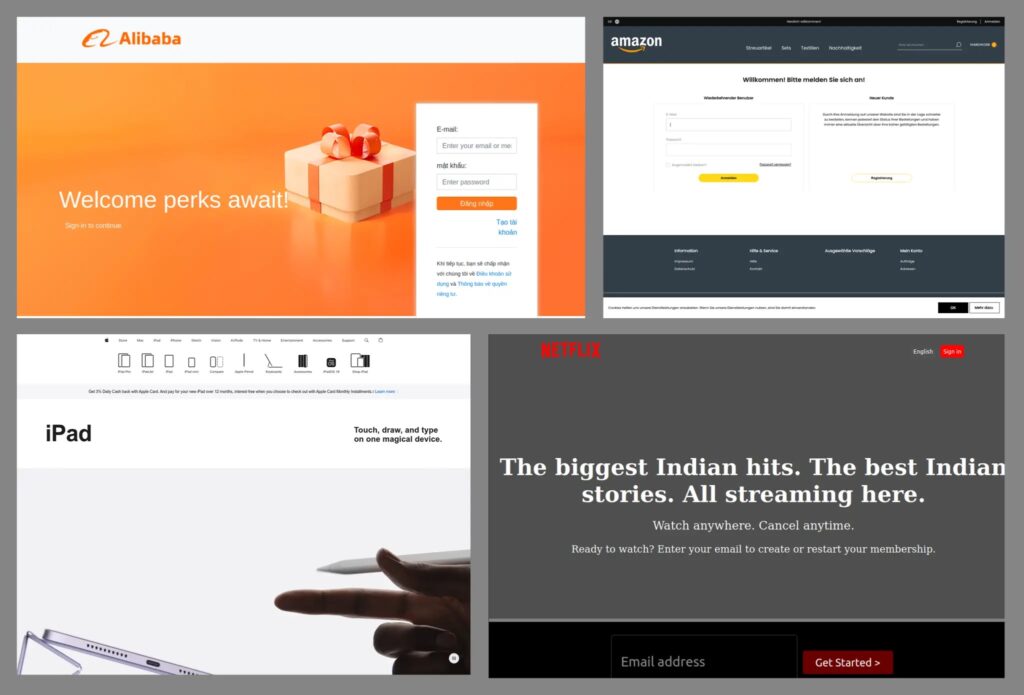
According to Securelist researchers, these banking trojans employ various deceptive techniques to trick users into installing the malware—ranging from simple social media lures like “Is that you in the picture?” to elaborate scams involving fake online stores and counterfeit delivery tracking apps.
Once installed, these trojans can steal credentials, intercept authentication codes, and execute unauthorized financial transactions, posing a severe risk to mobile banking security.
Geographic Targeting and Infection Mechanisms
Turkey remains the primary target of mobile banking malware, with 5.68% of Kaspersky mobile security users encountering financial threats—an increase of 2.7 percentage points from the previous year.
Other heavily targeted regions include Indonesia (2.71%), India (2.42%), and Azerbaijan (0.88%), highlighting the widespread reach of these cyber threats.
Infection Methods
The infection process typically starts with social engineering tactics designed to deceive users into downloading seemingly legitimate applications.
Mamont, for instance, spreads through fake app stores and direct downloads from phishing websites, tricking victims into installing the malware under the guise of trustworthy software.
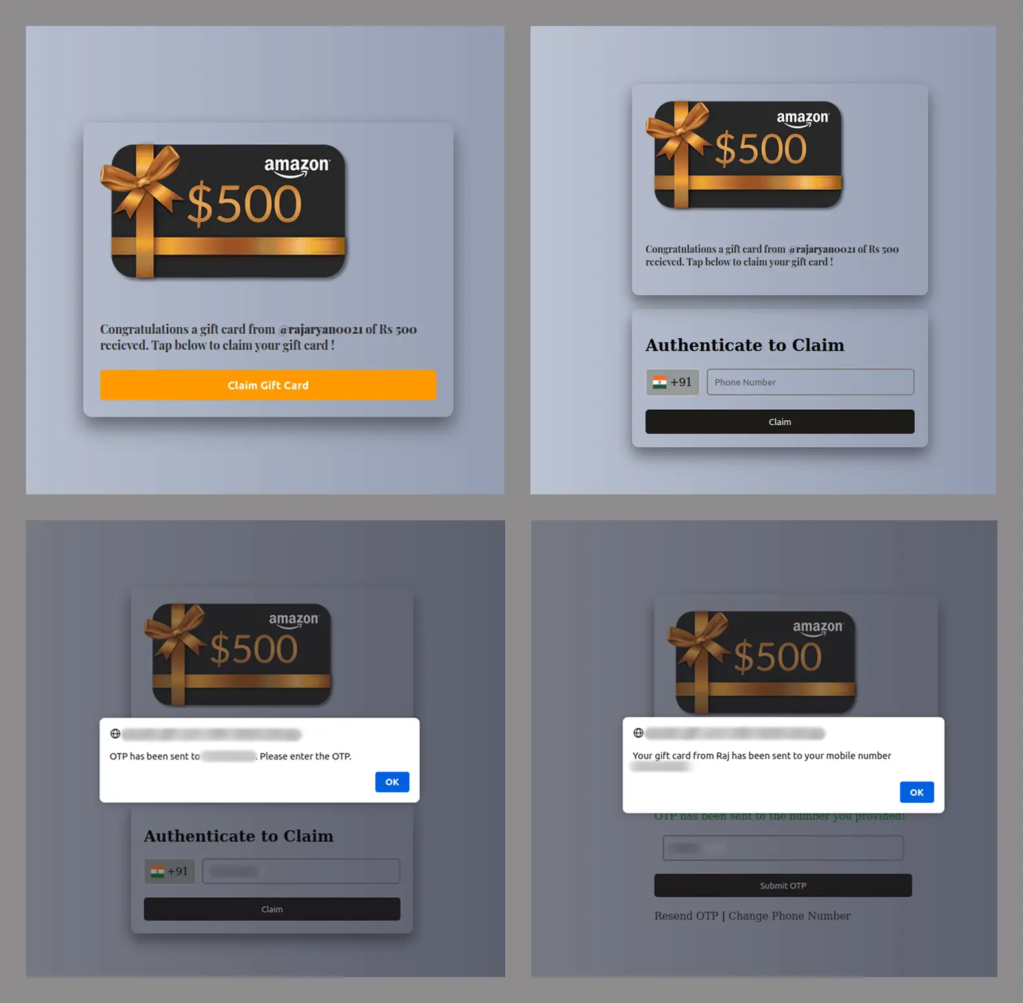
When victims install these applications, the malware requests extensive permissions, including SMS access, notification access, and accessibility services. These capabilities enable it to intercept authentication codes and overlay legitimate banking apps with phishing screens, tricking users into revealing sensitive information.
The malware operates using a straightforward yet highly effective command structure:
receive_sms {
if (message contains "verification" || "code" || "OTP") {
forward_to_command_server(message);
hide_message_from_user();
}
}
To stay protected, cybersecurity experts advise downloading apps only from official marketplaces, carefully reviewing permission requests, using trusted security solutions, and enabling multi-factor authentication (MFA) for financial accounts.












Post Comment