Malicious PyPI Packages Stole Cloud Tokens, Amassing Over 14,100 Downloads Before Removal
Cybersecurity researchers have uncovered a malicious campaign targeting users of the Python Package Index (PyPI) repository. Attackers have uploaded fraudulent libraries disguised as time-related utilities, concealing functionality designed to steal sensitive data, including cloud access tokens.
Software supply chain security firm ReversingLabs identified two groups of packages, totaling 20, which have collectively been downloaded over 14,100 times. These packages include:
- snapshot-photo (2,448 downloads)
- time-check-server (316 downloads)
- time-check-server-get (178 downloads)
- time-server-analysis (144 downloads)
- time-server-analyzer (74 downloads)
- time-server-test (155 downloads)
- time-service-checker (151 downloads)
- aclient-sdk (120 downloads)
- acloud-client (5,496 downloads)
- acloud-clients (198 downloads)
- acloud-client-uses (294 downloads)
- alicloud-client (622 downloads)
- alicloud-client-sdk (206 downloads)
- amzclients-sdk (100 downloads)
- awscloud-clients-core (206 downloads)
- credential-python-sdk (1,155 downloads)
- enumer-iam (1,254 downloads)
- tclients-sdk (173 downloads)
- tcloud-python-sdks (98 downloads)
- tcloud-python-test (793 downloads)
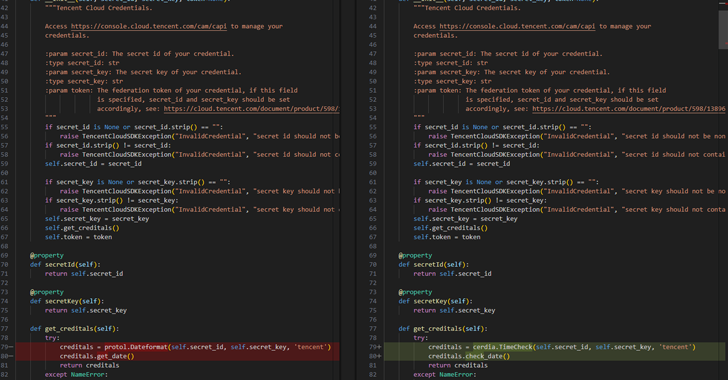
The first group consists of packages that facilitate data exfiltration to the threat actor’s infrastructure, while the second cluster includes packages mimicking cloud client functionalities for services such as Alibaba Cloud, Amazon Web Services (AWS), and Tencent Cloud.
But they have also been using “time” related packages to exfiltrate cloud secrets. All the identified packages have already been removed from PyPI as of writing.
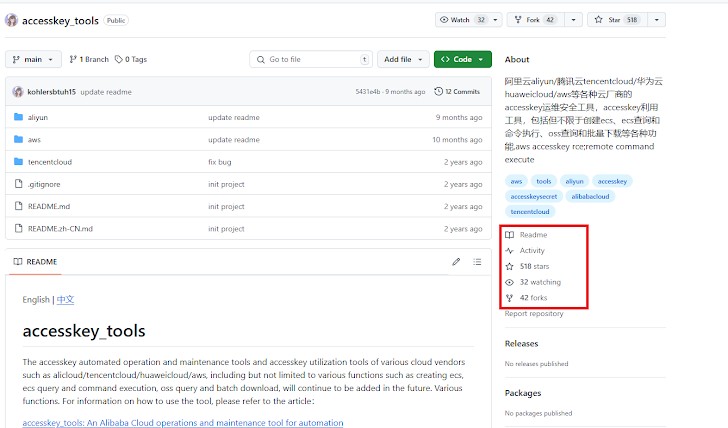
Further analysis has revealed that three of the packages, acloud-client, enumer-iam, and tcloud-python-test, has been listed as dependencies of a relatively popular GitHub project named accesskey_tools that has been forked 42 times and starred 519 times.
A source code commit referencing tcloud-python-test was made on November 8, 2023, suggesting that the package has been available for download on PyPI since then. According to pepy.tech, it has been downloaded 793 times to date.
This revelation comes as Fortinet FortiGuard Labs reports discovering thousands of suspicious packages across PyPI and npm. Some of these packages contain malicious install scripts designed to execute harmful code during installation or establish communication with external servers.
“Suspicious URLs are a key indicator of potentially malicious packages, as they are often used to download additional payloads or connect with command-and-control (C&C) servers, allowing attackers to take control of compromised systems,” said Jenna Wang.
She further noted that 974 packages were linked to data exfiltration, malware downloads, and other harmful activities, emphasizing the need for thorough scrutiny and monitoring of external URLs in package dependencies to prevent exploitation.











Post Comment