MassJacker Malware Exploits Piracy Users to Hijack Cryptocurrency Transactions
CyberArk researchers have uncovered a new malware campaign targeting users searching for pirated software. This campaign distributes a previously undocumented clipper malware known as MassJacker.
Clipper malware, classified as cryware by Microsoft, is designed to monitor a victim’s clipboard activity and facilitate cryptocurrency theft. It achieves this by replacing copied cryptocurrency wallet addresses with attacker-controlled ones, redirecting funds to the adversary instead of the intended recipient.
According to security researcher Ari Novick, the infection chain originates from a site called pesktop[.]com. “This site, which masquerades as a source for pirated software, also attempts to trick users into downloading various types of malware,” Novick explained in an analysis published earlier this week.
The attack begins with an initial executable that executes a PowerShell script, deploying the Amadey botnet malware along with two .NET binaries compiled separately for 32-bit and 64-bit systems.
One of these binaries, dubbed PackerE, downloads an encrypted DLL, which subsequently loads a second DLL. This second DLL then injects the MassJacker payload into a legitimate Windows process, “InstalUtil.exe,” ensuring its execution.
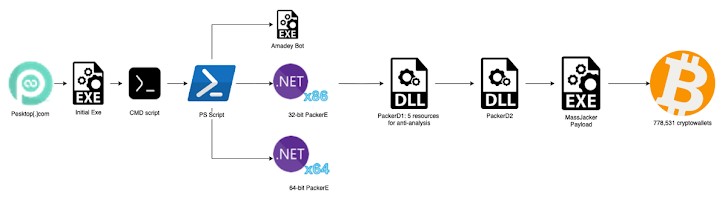
The encrypted DLL is designed with advanced evasion and anti-analysis techniques, including Just-In-Time (JIT) hooking, metadata token mapping to obscure function calls, and a custom virtual machine that interprets commands instead of executing standard .NET code.
MassJacker itself employs anti-debugging mechanisms and is configured to retrieve regular expression patterns used to detect cryptocurrency wallet addresses copied to the clipboard. Additionally, it connects to a remote server to download files containing a list of wallet addresses controlled by the threat actor.
“MassJacker creates an event handler that activates whenever the victim copies any content,” explained Novick. “The handler scans for cryptocurrency wallet patterns using regex, and if a match is found, it replaces the copied address with one from the attacker’s downloaded list.”
CyberArk’s analysis uncovered more than 778,531 unique wallet addresses associated with the attackers. Of these, only 423 wallets contained funds, amounting to approximately $95,300. However, the total value of digital assets initially stored across these wallets before being transferred out was estimated at $336,700.
Furthermore, investigators discovered a single wallet holding roughly $87,000 (600 SOL), with over 350 transactions funneling funds into it from various sources.
While the identity of the actors behind MassJacker remains unknown, an analysis of its source code has revealed similarities with MassLogger, another malware strain that also employs JIT hooking to evade analysis.












Post Comment