New BitM Attack Enables Hackers to Hijack User Sessions in Seconds
A newly emerging cyberattack technique, known as Browser-in-the-Middle (BitM), allows hackers to bypass multi-factor authentication (MFA) and hijack user sessions within seconds.
This attack exploits web browser functionalities to intercept authenticated sessions, posing a serious risk to organizations that rely on traditional security defenses.
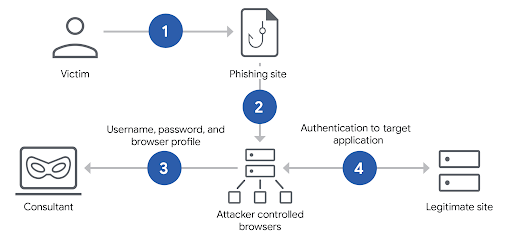
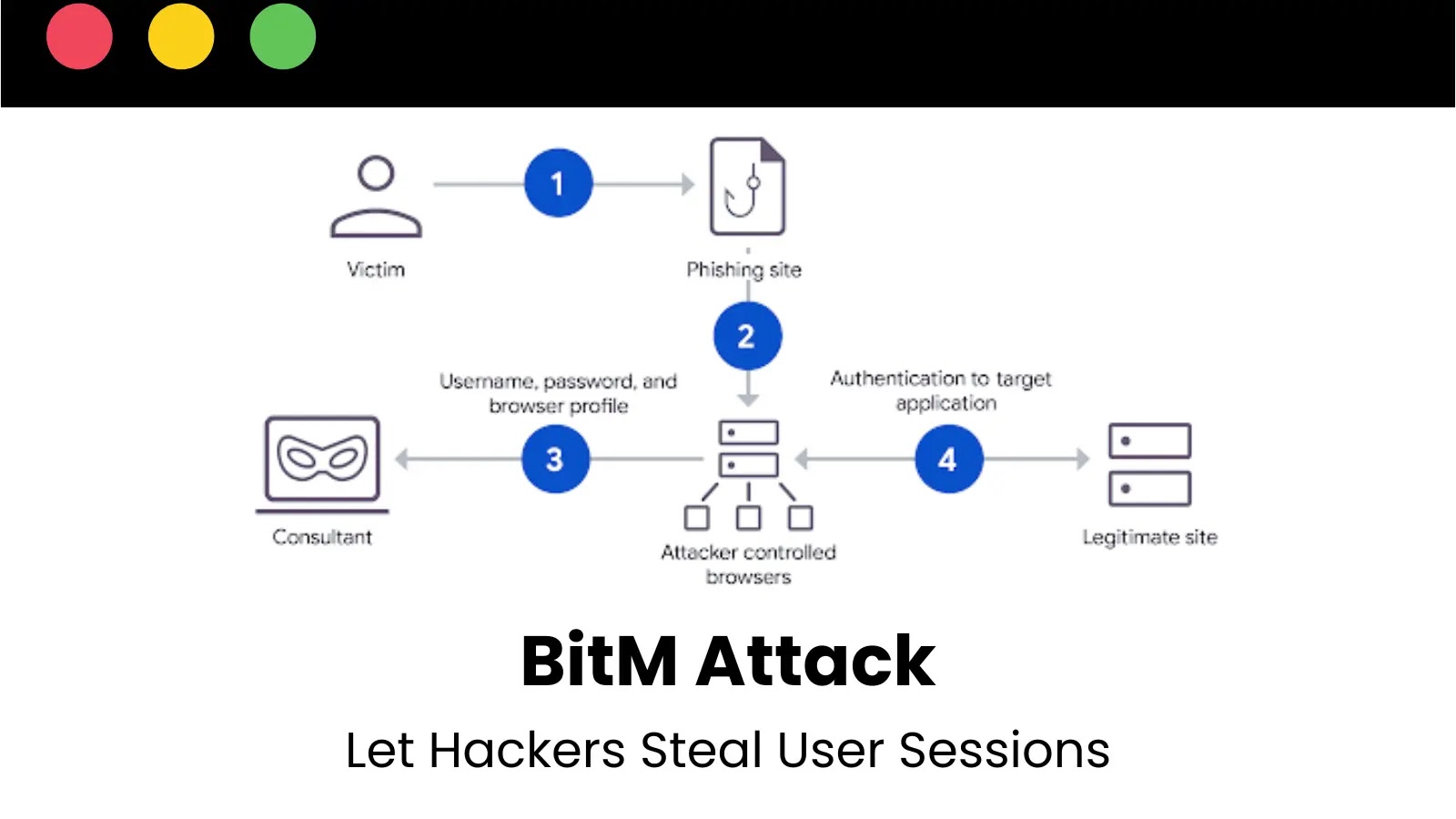
BitM attacks simulate a normal browsing experience by redirecting victims through an attacker-controlled browser. When a user visits a malicious site or clicks on a phishing link, their interactions are routed through a proxied browser hosted on the attacker’s server.
The attacker’s browser mimics the legitimate website, tricking users into entering credentials and completing MFA challenges. Once authentication is successful, the attacker captures the session token stored in the browser, granting them full access to the victim’s session.
Key Components of BitM Attacks
- Transparent Proxies: Tools like Evilginx2 and Mandiant’s internal tool, Delusion, serve as intermediaries between victims and target services. These proxies manipulate HTTP responses, replacing legitimate domains with phishing ones to extract session tokens.
- Rapid Deployment: Unlike traditional transparent proxies that require extensive configuration, BitM frameworks like Delusion enable attackers to quickly target any website. Features such as Firefox profile storage and automatic load balancing streamline large-scale phishing campaigns.
- Real-Time Monitoring: Attackers can track victim interactions live, allowing them to hijack sessions immediately after successful authentication.
BitM attacks are particularly dangerous because they circumvent multi-factor authentication (MFA), a security measure many organizations rely on as their last line of defense. By capturing session tokens, attackers gain persistent access to accounts without ever needing the victim’s credentials again, Google warned.
This technique is particularly effective against applications leveraging virtual desktop infrastructure (VDI) or cloud services, where session hijacking can provide attackers with privileged network access.
Corporate Security Risks
- Data Breaches & Takeovers: BitM attacks can lead to intellectual property theft, data breaches, and even full Active Directory compromises. Red teams frequently use these techniques to assess security weaknesses, exposing the risks of over-relying on MFA.
- Speed & Scalability: BitM tools, such as Delusion, streamline attack execution with container scaling and campaign management via tags, enabling large-scale phishing operations. Victims often remain unaware of the compromise until it’s too late.
Mitigating BitM Risks
While no system is completely immune, organizations can reduce their exposure through layered security measures:
- Hardware-Based MFA (FIDO2): Security keys like YubiKey or Google Titan enforce cryptographic authentication tied to specific domains, preventing attackers from replaying credentials across different sites.
- Client Certificates: Device-specific authentication certificates prevent stolen session tokens from being reused on unauthorized devices, reinforcing FIDO2 protections.
- Behavioral Monitoring: Security tools that analyze login patterns and browser fingerprint anomalies can detect potential BitM activity.
- Security Awareness Training: Educating employees on phishing indicators—such as suspicious URLs and unexpected authentication prompts—remains essential in minimizing risk.
BitM represents a significant evolution in cyber threats, leveraging browser functionalities to bypass traditional security controls. Given its speed and effectiveness, security teams worldwide must act swiftly to counter this emerging attack vector.











Post Comment