PJobRAT Malware Campaign Exploited Fake Chat Apps to Target Taiwanese Users
A previously identified Android malware family known for targeting Indian military personnel has resurfaced in a new campaign, this time likely targeting users in Taiwan under the guise of chat applications.
“PJobRAT can exfiltrate SMS messages, phone contacts, device and app details, documents, and media files from compromised Android devices,” Sophos security researcher Pankaj Kohli noted in an analysis published Thursday.
Originally documented in 2021, PJobRAT has been primarily deployed against Indian military-related targets. Over time, it has evolved, often disguising itself as dating and messaging apps to lure unsuspecting victims. However, its activity can be traced back to at least late 2019.
In November 2021, Meta attributed the use of PJobRAT and another malware, Mayhem, to SideCopy, a Pakistan-aligned threat actor believed to be a subgroup within Transparent Tribe. These attacks were highly targeted, focusing on individuals in Afghanistan linked to government, military, and law enforcement sectors.
According to Meta, the group crafted fake online personas—often presenting as young women—to establish trust with potential victims, ultimately deceiving them into clicking phishing links or installing malicious chat apps.
PJobRAT is designed to collect device metadata, contact lists, text messages, call logs, location data, and media files from both the device and any connected external storage. Additionally, it exploits accessibility services permissions to capture on-screen content.
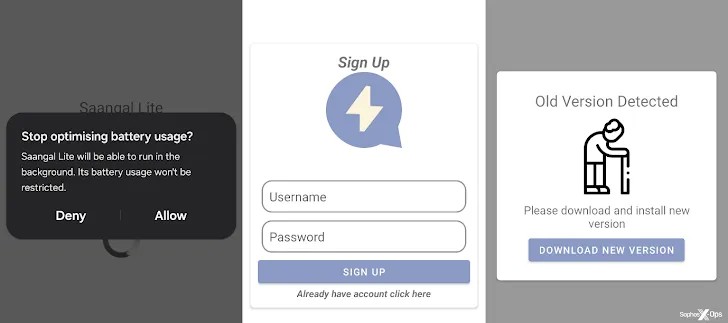
Sophos’ telemetry data indicates that the latest campaign specifically targets Taiwanese Android users. The attackers used trojanized chat apps, SangaalLite and CChat, to deliver the malware. These apps were reportedly distributed via multiple WordPress sites, with the earliest known sample dating back to January 2023.
According to the cybersecurity firm, the campaign concluded—or at least paused—around October 2024, after nearly two years of activity. Despite its duration, the number of infections remained relatively low, indicating a highly targeted operation. The identified Android package names used in the campaign include:
- org.complexy.hard
- com.happyho.app
- sa.aangal.lite
- net.over.simple
How victims were lured into visiting the malicious sites remains unclear. However, based on previous campaigns, social engineering likely played a role. Once installed, these apps request extensive permissions, enabling them to collect data and operate persistently in the background.
“The apps include basic chat functionality, allowing users to register, log in, and message each other. In theory, infected users could have unknowingly communicated with one another if they had each other’s user IDs,” said Sophos researcher Pankaj Kohli. “Additionally, the apps connect to command-and-control (C2) servers at startup to check for updates, allowing attackers to deploy new malware versions.”
Unlike earlier iterations of PJobRAT, which could extract WhatsApp messages, the latest version introduces the ability to execute shell commands. This enhancement likely enables attackers to access WhatsApp chats while also granting greater control over compromised devices.
Another key update involves the malware’s command-and-control mechanism. It now employs two methods: HTTP for uploading stolen data and Firebase Cloud Messaging (FCM) to send shell commands and exfiltrate information.
“While this campaign may have ended, it highlights how threat actors frequently refine their tactics, enhancing their malware and adjusting their approach before launching new attacks,” Kohli added.











Post Comment